Infrastructure:
Computer Networks
Parke Godfrey
9 September 2011
12 September 2011
CSE-2041
Credits
These slides are based on ones from the following sources.
- Prof. Hamzeh Roumani, CSE2041
- Prof. Natalija Vlajic, CSE3214
- J.F Kurose and K.W. Ross, Computer Networking, Addison-Wesley
- B. Forouzan, Data Communications and Networking, McGraw-Hill
- J. Jackson, Web Technologies: A CS Perspective, Prentice Hall
Outline
- Basics
- The Protocol Stack
- Network Security
- The Application Layer
Network Interface Controller (NIC)
-
Addresses
-
Each NIC has a MAC:
Media Access Control address (MAC address).
-
MAC is also known as the physical
or hardware address .
- MAC is a 48-bit integer.
-
That is, a 12 (= 48/4) hex-digit code.
-
The ipconfig command (ifconfig on Linux)
gives the MAC of the NIC.
- For example,
MAC = 00-1A-92-D3-D8-9E
Cables

- This is a twisted pair cable.
- This is a coaxial cable.

The physical medium that connects the NIC's can also be
fiber optics.
Or “nothing” in the case of wireless networks!
Different media have different costs, MBPS bandwidth, range,
and noise tolerance.
Local Area Network (LAN)

A LAN is made up of two or more nodes
(computers) whose NIC’s are connected.
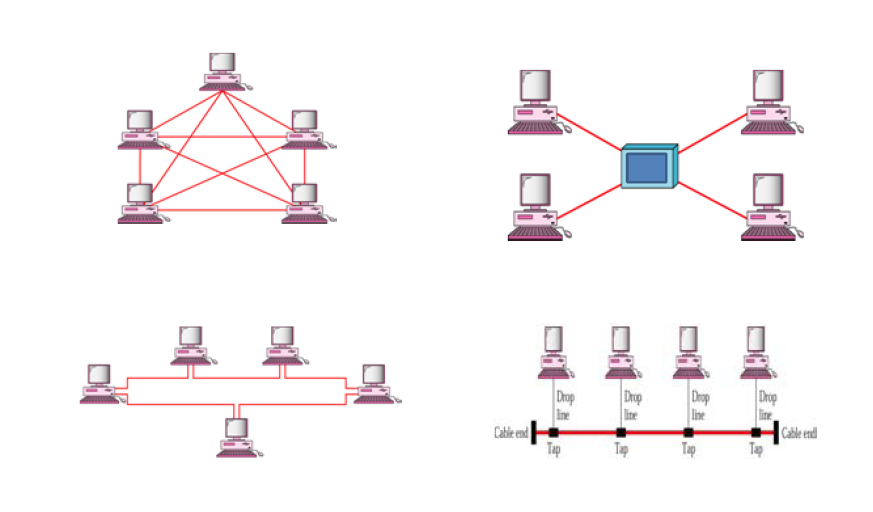
The connection topology can be mesh,
star, ring, or bus.
Network Topologies

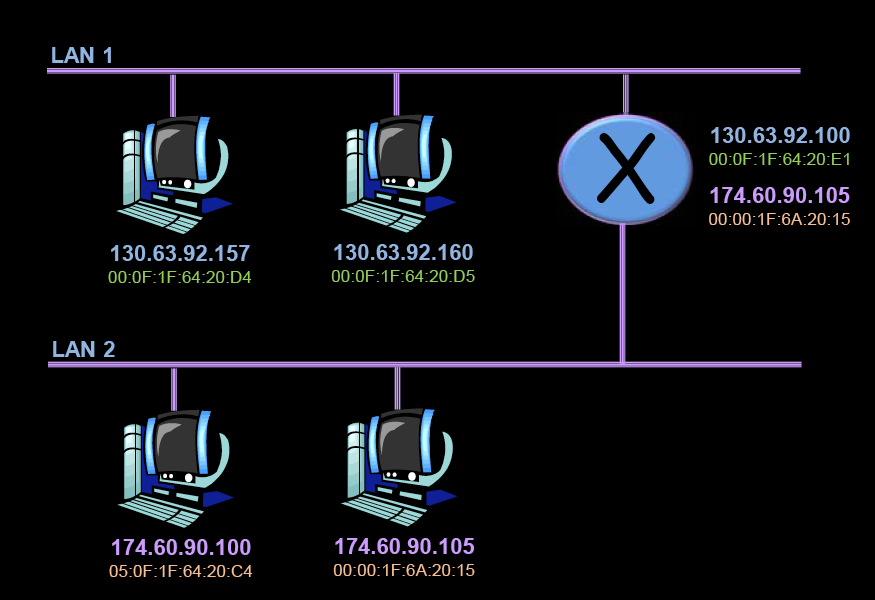
Unique MAC’s

Regardless of topology, no two nodes in
a LAN can have the same MAC.
Computers in the LAN can thus address
each using their MAC’s.
Inter-Networking

Connecting two LAN’s requires two things.
- The two LAN’s must share a node.
That node would have two NIC’s.
- We need an addressing mechanism that goes beyond MAC’s.
IP Addresses

- A router is a computer with two
NIC’s connected to two LAN’s.
- An
IP address
is a 32-bit integer
that is unique across LAN’s.
32 bit = 4 x 8 bits
= 4 x (int between 0 and 255)
Example: 130.63.236.137
Aside:
The above is IPv4.
But the world is running out of IP addresses!
Slowly and painfully,
everything will migrate over to
IPv6
over the next several years.
Between LAN’s

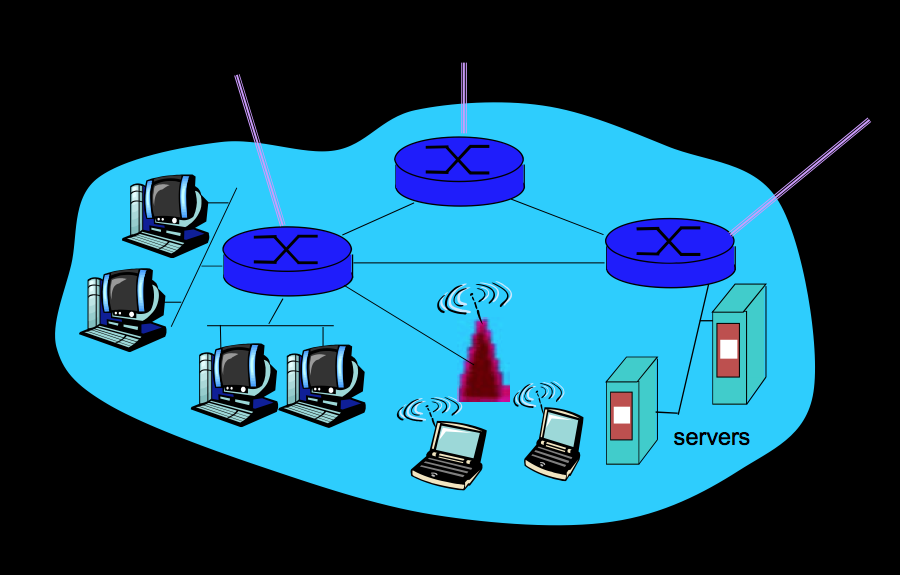
Typical University Network

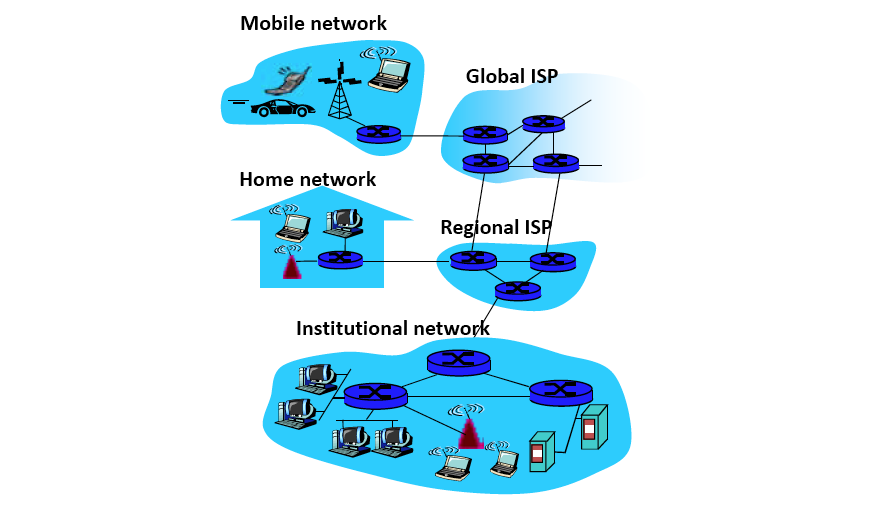
The Internet

Internet Trunks

Orion

Outline
- Basics
- The Protocol Stack
- Network Security
- The Application Layer
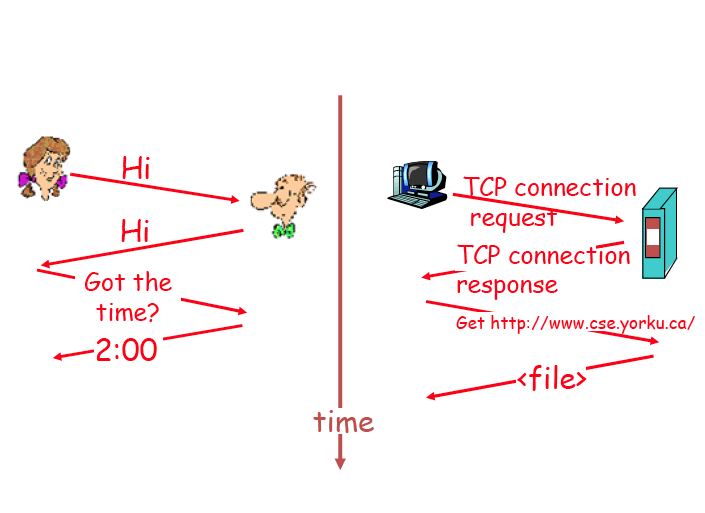
Protocols

Rules that governs the communication of data
between computers. They involve:
- Syntax
- Format of data units, e.g. number and size of fields in
a packet and how are they delimited.
- Semantics
- Meaning associated with the bits carried in control fields.
- Timing
- When data should be sent and how fast.
Protocol Example
Abstraction!

- Communication in the Internet involves so many
issues and deals with heterogeneous entities.
- To confront this complexity, we use abstraction.
- Each layers hides the details under it. It appears
as a service to the layer above it.
- Separation of concerns: an implementer at one
level is not concerned with issues at other levels.
- Same strategy as separating class usage from its
implementation in OOP.
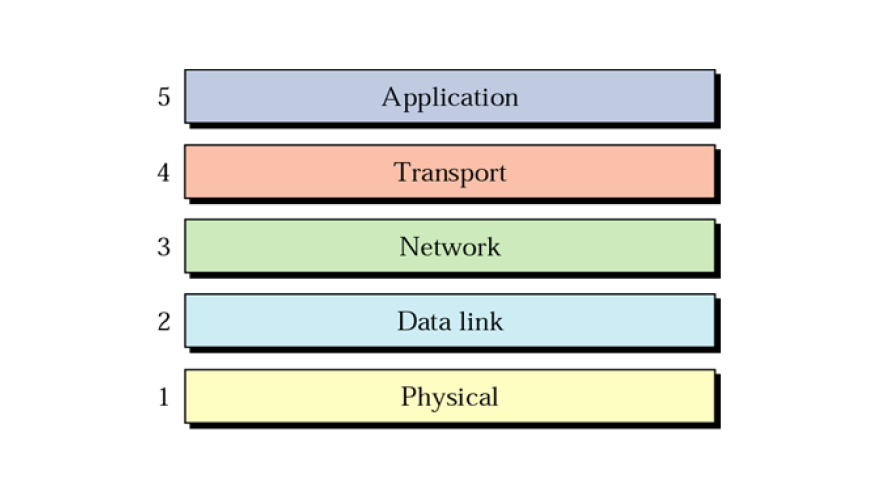
The Internet Protocol Suite

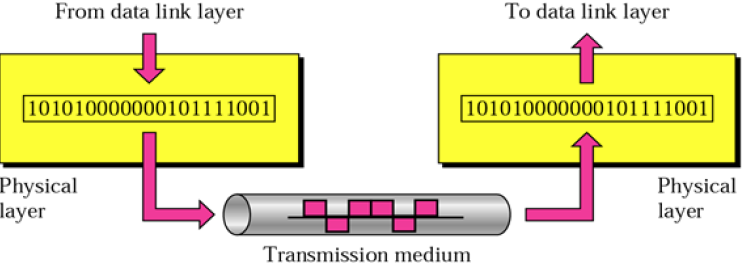
The Physical Layer
- Responsibility
- Transmitting one bit from the NIC to the medium
- Data Unit
- Issues
- Signal Encoding (how to represent a bit on the medium)
- Protocols
- Ethernet, 802.11 (WiFi), Firewire, …
- Addressing
The Physical Layer

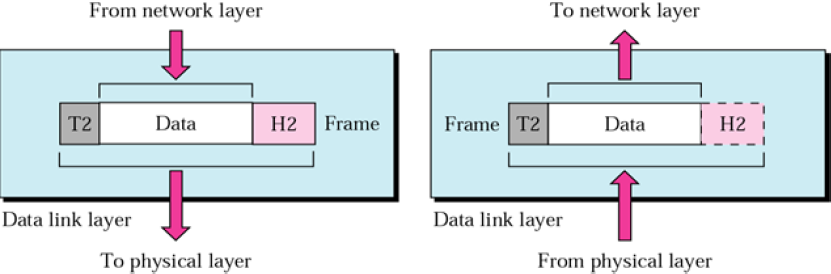
The Data Link Layer
- Responsibility
- Transmitting frames from one node to another on the same LAN.
- Data Unit
- Issues
- Error control and access control.
- Protocols
- Ethernet, 802.11 (WiFi), ARP (and RARP), …
- Addressing
- Via from/to MAC addresses.
The Data Link Layer

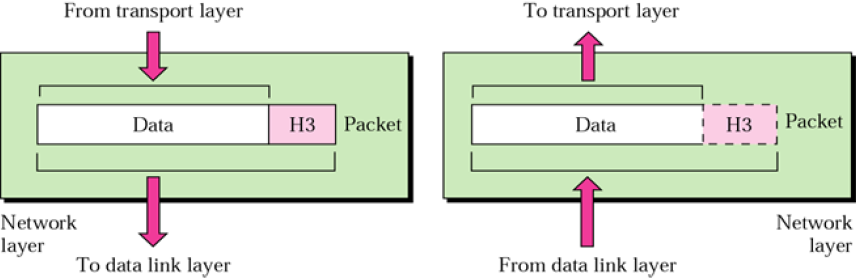
The Network Layer
- Responsibility
- Transmitting packets from a node in one LAN to a
node in another LAN.
- Data Unit
- Issues
- Protocols
- IP (v4/v6), IPsec, ICMP, ATM, …
- Addressing
- Via from/to IP addresses.
The Network Layer

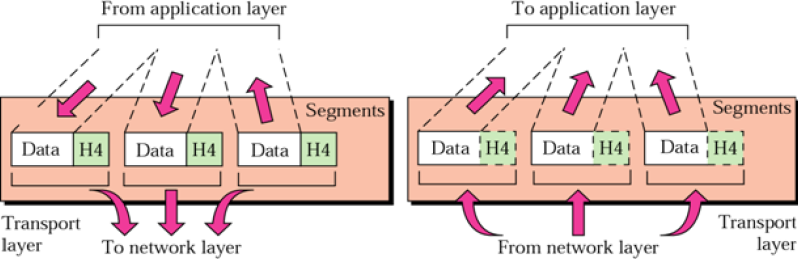
The Transport Layer
- Responsibility
- Transmitting messages from a process running on a node
in one LAN to one running on a node in another LAN.
- Data Unit
- Issues
- Error control, flow control, reordering
- Protocols
- Addressing
- Via from/to PORT number (a 16-bit integer).
The Transport Layer

Ports

A process can associate itself with any port number but most
port numbers below 1024 are reserved.
E.g.,
- 20 / 21 for FTP,
- 22 for SSH,
- 23 for Telnet,
- 25 for SMTP,
- 53 for DNS,
- 80 / 443 for HTTP / HTTPS.
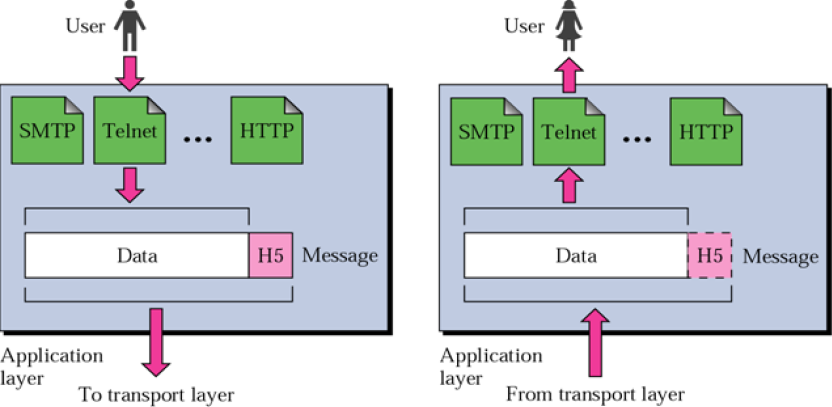
The Application Layer
- Responsibility
- Providing services to the end user.
- Data Unit
- Issues
- Synchronization, encryption, logging, compression, …
- Protocols
- HTTP, DNS, FTP, SSH, TELNET, SMTP, JDBC, SOAP, …
- Addressing
- URL:
scheme://host:port/path;extra?query#fragment
The Application Layer

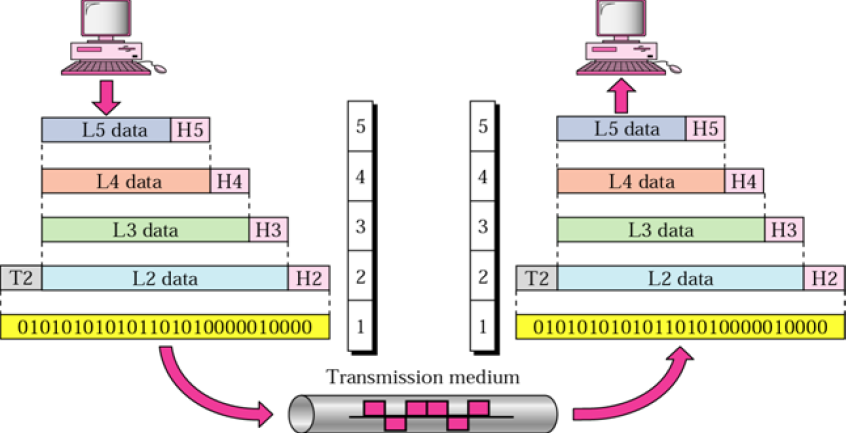
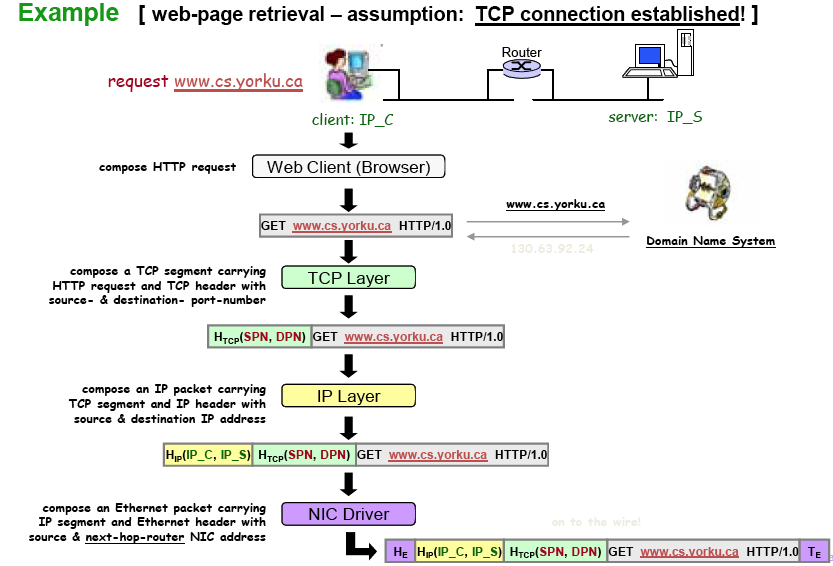
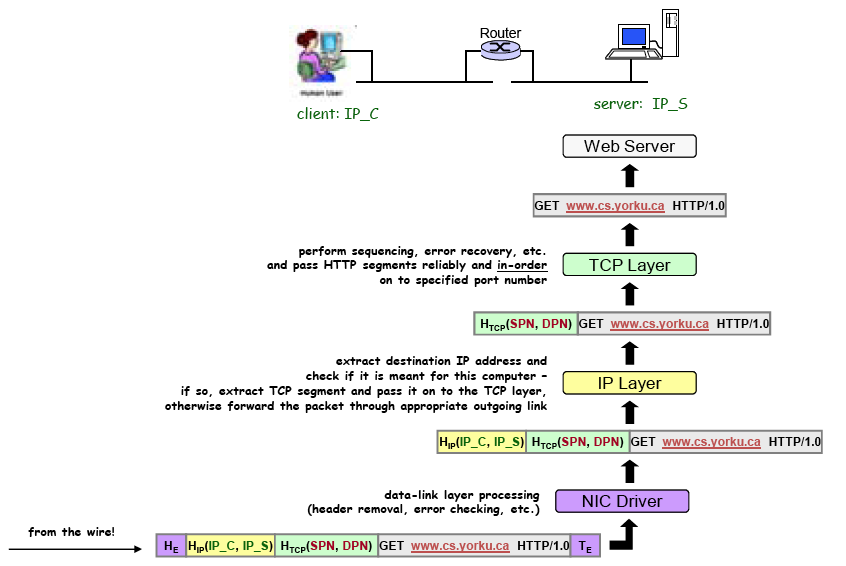
Header Addition & Removal

TCP/IP Protocol:
How the Layers Work Together

TCP/IP Protocol:
How the Layers Work Together (p.2)

The Protocol Stack
Five or Seven Layers?

The
Internet Protocol suite
is usually described as these five layers.
The
OSI Model
describes seven layers.
Essentially, its first four are the same as the Internet Protocol suite's.
OSI divides our application layer further into three layers:
- Session Layer,
- Presentation Layer, and
- Application Layer.
Much of our focus in this course is
in the Internet Protocol suite's application layer.
Outline
- Basics
- The Protocol Stack
- Network Security
- The Application Layer
Network Security
Why is network security much of an issue?
Wouldn't the design of the “Internet”
have designed in security from the beginning?!
Well...
Like a city's infrastructure,
individual pieces are often well designed at the start
(e.g., highway systems, sewage, zoning).
But much evolves over time.
- system complexity.
How the pieces operate together is very complex.
- legacy.
We build on existing infrastructure.
- usage.
How things are actually used changes over time.
- Original design goals may no longer make sense.
- Scalability.
Network Security
Issues
- Need to identify
-
vulnerabilities, threats, possible attacks,
and attackers' motivation.
- Must devise countermeasures to
- deter,
detect,
block,
log, and
recover.
- Attack vectors:
- Our goals:
- confidentiality,
integrity,
availability, and
authentication.
Malware

Trojan horse
- Hidden part of some otherwise useful software.
- Today, often on a Web page (e.g., Active‐X, plugin).
Worm
- Infection by passively receiving object
that gets itself executed.
- Self‐replicating: propagates to other hosts, users.

Spyware
- Can record keystrokes and then upload info to collection site.
- Can use cookies and other local objects to track visits.
Virus
- infection by actively executing a received object
(e.g., attachment).
- Self‐replicating: propagates to other hosts, users.
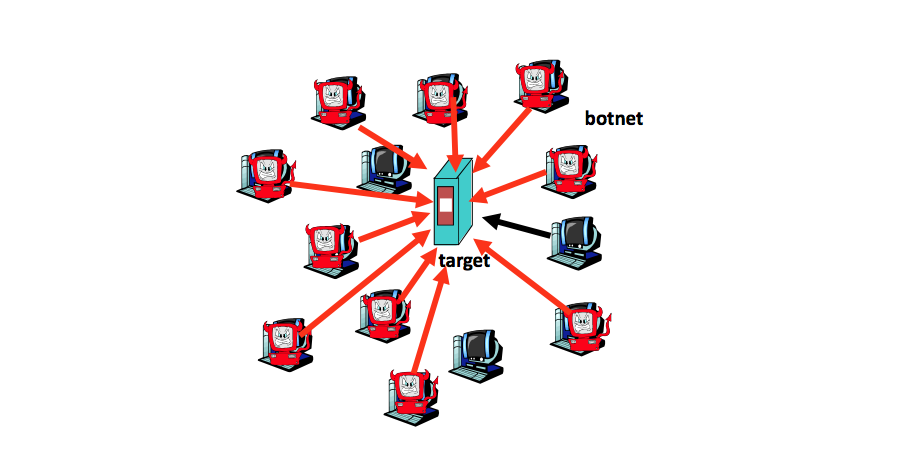
D-DOS: Distributed-denial-of-service attack

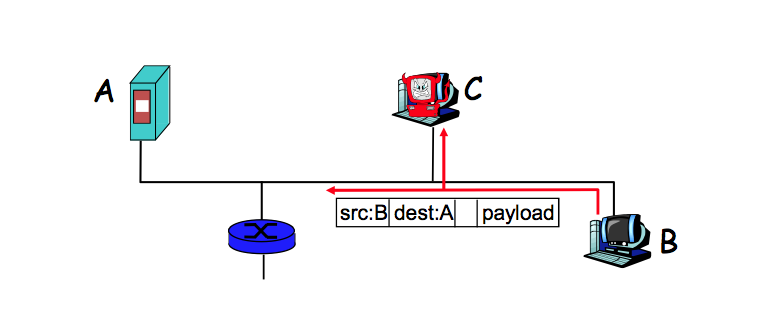
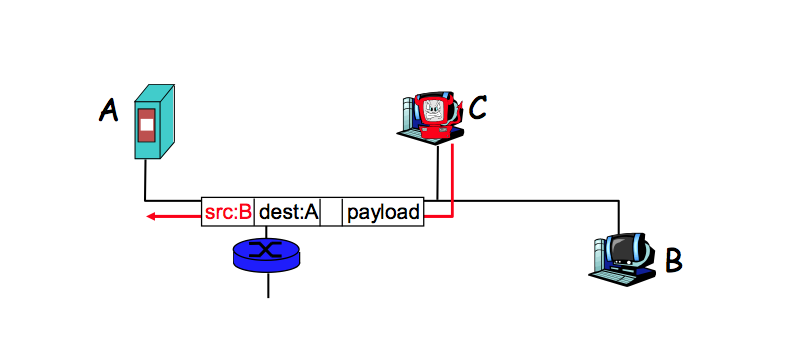
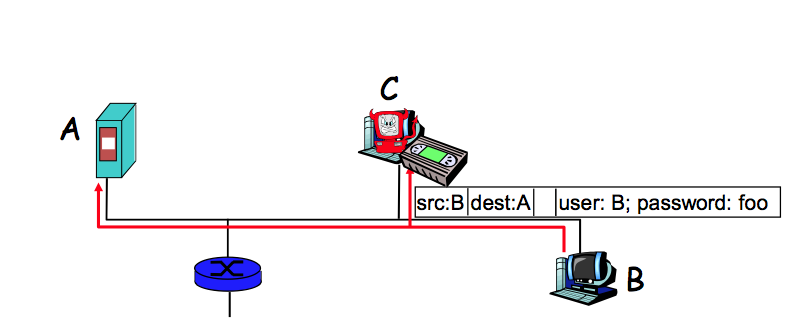
Packet Sniffing

Works in
- broadcast media (wireless), and
- promiscuous NIC mode
IP Spoofing

Simply change the IP-level header.
Replay

Sniff password, then masquerade.
Outline
- Basics
- The Protocol Stack
- Network Security
- The Application Layer

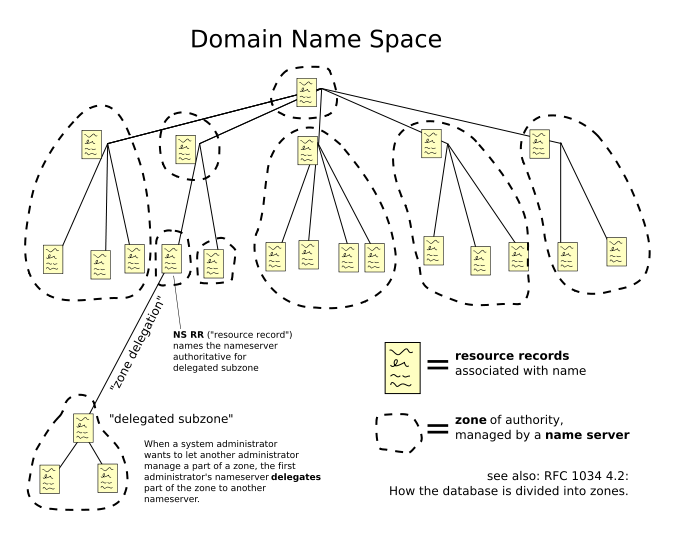
Problems with IP addresses:
- For people and applications to need to use IP addresses would be painful,
since the numbers are not meaningful.
- IP addresses can be reassigned, can change.
DNS is a hierarchical distributed naming system
for NIC's
that maps names to IP addresses.
The Internet's name-space is overseen by
ICANN (the Internet Corporation for Assigned Names and Numbers).
“DNS” is also an application layer service.
The Application Layer
DNS

HTTP is the application layer protocol
for what we call
the World Wide Web
(also called the WWW, W3, or the Web).
History
So... The Internet ≠ The Web
- The Internet
- ARPANET: late 1960's
- TCP/IP: in the 1970's
- e-mail: 1972
- NSFNET: 1985 – 1995
-
- 1995 – : privately funded (ISP's, etc.)
- The WWW
- Proposed in 1989 at CERN by Sir Tim Berners-Lee.
- Went “live” on 6 August 1991.